Enhancing Cyber-Physical System Security through Intrusion Detection and Response Mechanisms
Table Of Contents
<p><br>Table of Contents:<br><br>1. Introduction<br> 1.1 Background<br> 1.2 Evolution of Cyber-Physical Systems (CPS)<br> 1.3 Significance of Security in CPS<br> 1.4 Research Motivation<br> 1.5 Research Objectives<br> 1.6 Research Scope<br> 1.7 Organization of the Thesis<br><br>2. Literature Review<br> 2.1 Overview of Cyber-Physical Systems<br> 2.2 Security Threats and Vulnerabilities in CPS<br> 2.3 Intrusion Detection Systems for CPS<br> 2.4 Response Mechanisms in CPS Security<br> 2.5 Current Approaches to CPS Security<br> 2.6 Best Practices in Intrusion Detection and Response<br> 2.7 Related Work in CPS Security and Intrusion Response<br><br>3. Methodology<br> 3.1 Analysis of Security Requirements in Cyber-Physical Systems<br> 3.2 Selection of Intrusion Detection Techniques<br> 3.3 Design of Response Mechanisms and Protocols<br> 3.4 Simulation and Experimentation Setup<br> 3.5 Performance Metrics for Intrusion Detection and Response<br> 3.6 Ethical Considerations in CPS Security Research<br> 3.7 Data Collection and Preprocessing for Intrusion Analysis<br><br>4. Implementation and Results<br> 4.1 Development of Intrusion Detection System for CPS<br> 4.2 Integration of Response Mechanisms and Protocols<br> 4.3 Experiment Design and Execution<br> 4.4 Analysis of Intrusion Detection and Response Performance<br> 4.5 Comparison with Existing Security Measures<br> 4.6 Visualization of Security Enhancements in CPS<br> 4.7 Discussion of Results and Findings<br><br>5. Conclusion and Future Work<br> 5.1 Summary of Research Contributions<br> 5.2 Implications of the Study<br> 5.3 Limitations of the Research<br> 5.4 Future Research Directions in CPS Security<br> 5.5 Practical Applications and Industry Relevance<br> 5.6 Recommendations for Enhancing CPS Security<br> 5.7 Conclusion and Final Remarks<br><br><br></p>
Project Abstract
Abstract
Cyber-Physical Systems (CPS) integrate computational and physical processes, making them vulnerable to various security threats. This research focuses on enhancing CPS security through the implementation of effective intrusion detection and response mechanisms. The study begins with a comprehensive review of CPS, security threats, and existing approaches to security measures. A detailed methodology for security requirements analysis, intrusion detection technique selection, and response mechanism design is presented. The implementation phase involves the development of an intrusion detection system for CPS, integration of response mechanisms, and performance evaluation. The results are analyzed, compared with existing security measures, and visualized to demonstrate the security enhancements achieved. The thesis concludes with a summary of research contributions, implications, and recommendations for future work in the field of enhancing CPS security through intrusion detection and response mechanisms. This research is expected to provide valuable insights and practical solutions for addressing security concerns in CPS.
Project Overview
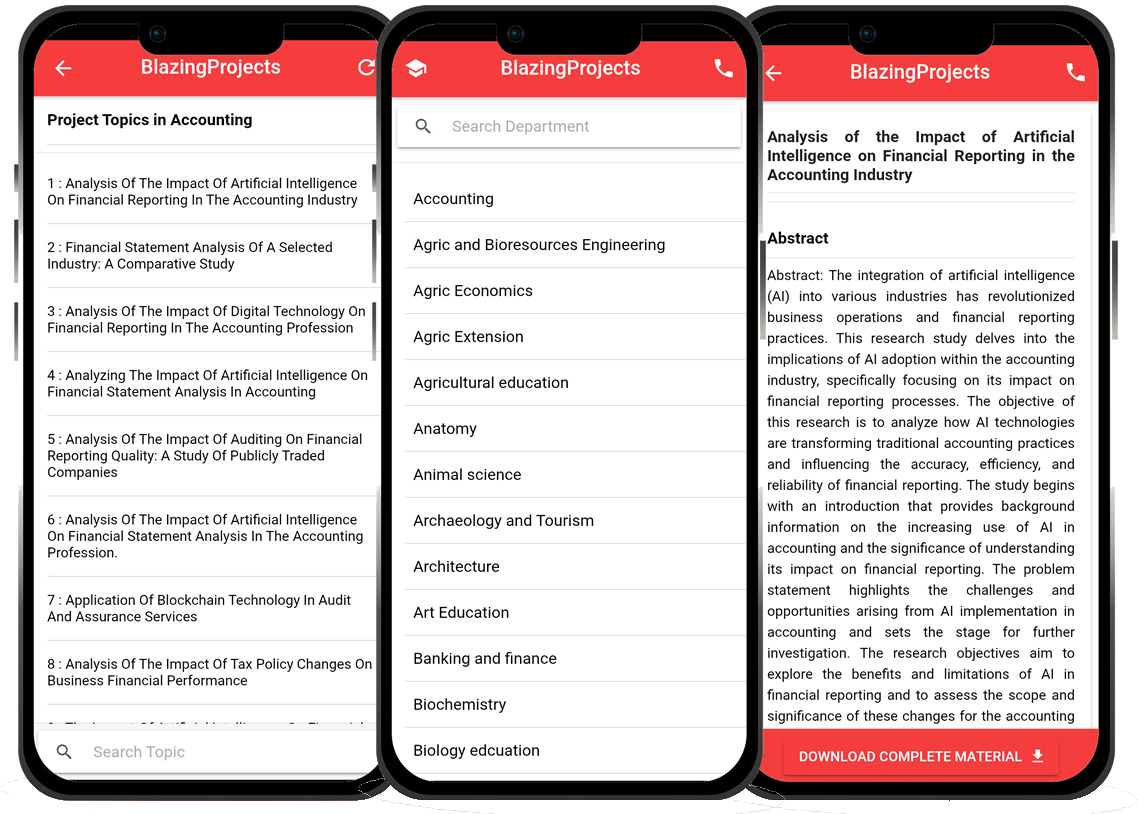
Blazingprojects Mobile App
📚 Over 50,000 Project Materials
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Software coding and Machine construction
🎓 Postgraduate/Undergraduate Research works
📥 Instant Whatsapp/Email Delivery
Related Research
Predicting Disease Outbreaks Using Machine Learning and Data Analysis...
The project topic, "Predicting Disease Outbreaks Using Machine Learning and Data Analysis," focuses on utilizing advanced computational techniques to ...
Implementation of a Real-Time Facial Recognition System using Deep Learning Techniqu...
The project on "Implementation of a Real-Time Facial Recognition System using Deep Learning Techniques" aims to develop a sophisticated system that ca...
Applying Machine Learning for Network Intrusion Detection...
The project topic "Applying Machine Learning for Network Intrusion Detection" focuses on utilizing machine learning algorithms to enhance the detectio...
Analyzing and Improving Machine Learning Model Performance Using Explainable AI Tech...
The project topic "Analyzing and Improving Machine Learning Model Performance Using Explainable AI Techniques" focuses on enhancing the effectiveness ...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project topic "Applying Machine Learning Algorithms for Predicting Stock Market Trends" revolves around the application of cutting-edge machine le...
Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project topic, "Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems," focuses on the integration of machine learn...
Anomaly Detection in Internet of Things (IoT) Networks using Machine Learning Algori...
Anomaly detection in Internet of Things (IoT) networks using machine learning algorithms is a critical research area that aims to enhance the security and effic...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
Anomaly detection in network traffic using machine learning algorithms is a crucial aspect of cybersecurity that aims to identify unusual patterns or behaviors ...
Predictive maintenance using machine learning algorithms...
Predictive maintenance is a proactive maintenance strategy that aims to predict equipment failures before they occur, thereby reducing downtime and maintenance ...