Design and implementation of claim based biometric authentication system over the cloud
Table Of Contents
<p> </p><p><b>DICLARATION OF ORIGINALITY – – ii </b></p><p><b>ABSTRACT – – – iii </b></p><p><b>صÙختسÙÙا – – – iv </b></p><p><b>ACKNOWLEDGEMENT – v </b></p><p><b>DEDICATION – vi </b></p><p><b>TABLE OF CONTENTS – – – vii </b></p><p><b>LIST OF FIGURES – – – ix </b></p><p><b>LIST OF ABBREVIATIONS – – – xi </b></p><p><b>1 INTRODUCTION – – 1 </b></p><p>11 Introduction – – – 1 </p><p>12 Project Background – – – 1 </p><p>13 Problem Statement – – 1 </p><p>14 Motivation – 1 </p><p>15 Objectives – 2 </p><p>16 Thesis Layout – – 2 </p><p><b>2 LITERATURE REVIEW – – – 3 </b></p><p>21 Introduction – – – 3 </p><p>22 Authentication – – – 3 </p><p>23 Biometrics – 4 </p><p>231 Generic biometric authentication system – – – – _ 5 </p><p>232 Fingerprint biometrics – – – – – 6 </p><p>2321 Fingerprint characteristics – – – 6 </p><p>2322 Issues in fingerprint recognition technology – – 7 </p><p>233 Face biometrics – – – – – 8 </p><p>2331 Processing workflow – 8 </p><p>24 Software Architectural Concepts – – 9 </p><p>241 Claims-Based Authentication and Identity Providers – – – _ 9 </p><p>2411 Components of the claim-based authentication – – 10 </p><p>2412 Claims-based authentication standards – – 12 </p><div>2<p></p><p>413 Token format standard : Security Assertion Markup Language 20 (SAML 20) – – 12 </p></div><p>242 Service oriented Architecture – – – – – 13 </p><p>243 Model-View-Controller (MVC) – – – – 14 </p><p>2431 Components interaction – – – 15 </p><p>25 Programming Languages, Platforms, Technologies and Tools – 16 </p><p>251 Programming languages – – – – _ 16 </p><p>252 Platforms – – – – – – 16 </p><p>253 Technologies – – – – – _ 16 </p><p>254 Tools – – – – – – 18 </p><p><b>3 METHODOLOGY – – – 20</b> </p><p>31 Introduction – – 20 </p><p>32 Project Initiation – 20 </p><p>33 Project Planning – 22 </p><p>331 Scope planning – – – – – _ 22 </p><p>332 Time planning – – – – – 22 </p><p>333 Risk management planning – – – – – 23 </p><p>34 Project Execution – – 23 </p><p>341 Software requirements – – – – – 24 </p><p>342 Software design – – – – – _ 24 </p><p>3421 BioSTS – – – 25 </p><p>3422 Employees Administration Module – – 35 </p><p>3423 Employees Access Module – 37 </p><p>3424 Security Issues – – 37 </p><p>35 Project Monitoring and Controlling – – 38 </p><p>36 Project Closing – – 38 </p><p><b>4 IMPLEMENTATION AND RESULTS – – 39 </b></p><p>41 Introduction – – 39 </p><p>42 Software Construction – – 39 </p><p>421 BioSTS – – – – – 39 </p><p>422 Employees Administration Module – – – – – 43 </p><p>423 Employees Access Module – – – – – 45 </p><p>43 Software Verification – – – 47 </p><p>44 Software Deployment – – – 47 </p><p><b>5 CONCLUSION AND FUTURE WORK – – 48 </b></p><p>51 Project Review – – 48 </p><p>52 Limitations – – – 48 </p><p>53 Future Work – – – 49 </p><p><b>BIBLIOGRAPHY – – – 50 </b></p><p><b>Appendix A :</b> Project Management Documents – – A-1 </p><p><b>Appendix B : </b>Software Engineering Documents – B-1 </p><p> </p><p><b> LIST OF FIGURES </b></p><p> </p><p>Figure 2-1 Generic biometric authentication system – 6 </p><p>Figure 2-2 Fingerprint points types – – 7 </p><p>Figure 2-3 Face recognition system processing workflow – – – 8 </p><p>Figure 2-4 Claims-based identity workflow – – 9 </p><p>Figure 2-5 The format of the token – – 10 </p><p>Figure 2-6 How does the STS works – – 11 </p><p>Figure 2-7 The complete scenario of the claims-based authentication – – 11 </p><p>Figure 2-8 SAML 20 token format – – 13 </p><p>Figure 2-9 Service components – – 14 </p><p>Figure 2-10 MVC design pattern – – 15 </p><p>Figure 2-11 Internet connectivity challenges – – 17 </p><p>Figure 2-12 The service bus as a relay service – – 18 </p><p>Figure 3-1 Project management lifecycle and software development lifecycle overlapping – – 21 </p><p>Figure 3-2 Project time plan â“ page 1 – – 22 </p><p>Figure 3-3 Project time plan â“ page 2 – – 23 </p><p>Figure 3-4 The high level architecture of the system – – 24 </p><p>Figure 3-5 The STS process workflow – – 25 </p><p>Figure 3-6 IdentityServer architecture – – 26 </p><p>Figure 3-7 Data flow used by UareU SDK in fingerprint recognition – 28 </p><p>Figure 3-8 Transmitting the fingerprint as FMD over a network – – 29 </p><p>Figure 3-9 Fingerprint enrollment/authentication block diagram – – 29 </p><p>Figure 3-10 Face recognition REST API description – – 30 </p><p>Figure 3-11 Face detection REST API description – – 31 </p><p>Figure â 3-12 Tags saving REST API description – – 31 </p><p>Figure â 3-13 Faces training REST API description – – 31 </p><p>Figure 3-14 Face recognition enrollment flow chart – – 32 </p><p>Figure 3-15 Face recognition authentication flow chart – – – 33 </p><p>Figure 3-16 Overall authentication process workflow – 34 </p><p>Figure 3-17 Employee enrollment use case – – 36 </p><p>Figure 3-18 Modify employeeâs enrollment use case – – 36 </p><p>Figure 3-19 Change employeeâs fingerprint use case – – 36 </p><p>Figure 4-1 BioSTS architecture – 39 </p><p>Figure 4-2 The customized users store – – 40 </p><p>Figure 4-3 The UserRepository Class – – 40 </p><p>Figure 4-4 The ClaimsRepository class – – 41 </p><p>Figure 4-5 Fingerprint authentication user interface – – 41 </p><p>Figure 4-6 Face authentication user interface – – 42 </p><p>Figure 4-7 The BioSTS Users Repository Service – 42 </p><p>Figure 4-8 Configure the Employees Administration Module to trust BioSTS – – 43 </p><p>Figure 4-9 The Administration module employees list – – 43 </p><p>Figure 4-10 The Administration module employee profile modification – 44 </p><p>Figure 4-11 Administration Module Service – – 44 </p><p>Figure 4-12 âAdministration Module Serviceâ service bus configuration – 45 </p><p>Figure 4-13 Employees Access module home page – – 45 </p><p>Figure 4-14 Employee information page – – 46 </p><p>Figure 4-15 Employees Access Service – – 46 </p><p>Figure 4-16 Employees Access Service service bus configuration – – 46 </p><p> </p><p><b>LIST OF ABBREVIATIONS </b></p><p> </p><p><b>IIS </b> Internet Information Services </p><p><b>NAT </b> Network Address Translation </p><p><b>SOA </b> Service Oriented Architecture </p><p><b>SAML</b> Security Assertion Markup Language </p><p><b>WIF</b> Windows Identity Foundation </p><p><b>WCF</b> Windows Communication Foundation </p><p><b>SDLC</b> Software Development Life Cycle </p><p><b>RP</b> Relying Party </p><p><b>STS</b> Security Token Service</p> <br><p></p>
Project Abstract
In spite of their widespread use and ubiquity, passwords are unreliable as an
authentication methodology because they can be hacked or even guessed, yet when it comes to
biometrics it is very hard to impersonate someone. Therefore, biometric authentication schemes
are currently widely recognized as the strongest authentication technologies available on the
market.
Identity providers and claims-based identity are emerging technologies that aims to
decouple the authentication logic from the applicationâs business logic. This can be done by
assigning the authentication task to the identity provider and establishing a trust relationship
between the application and the identity provider so that the application relies on the identity
provider to authenticate the application users.
The project aims to develop an identity provider that uses fingerprint and facial
biometrics to authenticate users. The identity provider task is to determine the identity of the user
and pass the identity information to the relying applications which trust this identity provider.
For security purposes, the biometrics data of users is stored on a local server within the
sponsoring companyâs intranet. This local server is located behind firewalls and itâs address can
only be resolved internally within the intranet due to use of NAT. Therefore, the server doesnât
have a global IP address. Windows Azure cloud platform has a powerful component called
âWindows Azure Service Busâ which was used to solve this tough connectivity problem.
The project also aims to develop a simple employees management application that can be
used as an example of a relying application that relies on the developed identity provider to
authenticate the users.
Project management principles and software development lifecycle techniques were
applied during the project implementation. This approach has significantly streamlined the
project implementation process and the project objectives have been met.
Project Overview
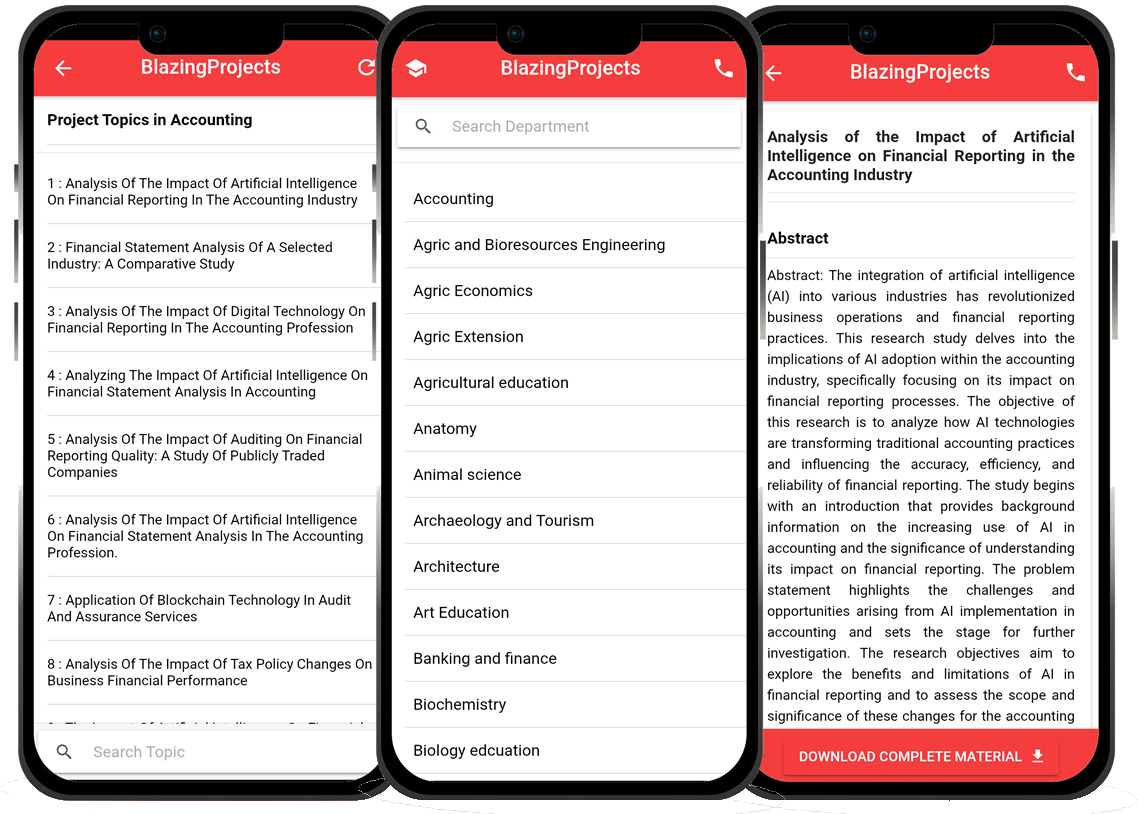
Blazingprojects Mobile App
📚 Over 50,000 Project Materials
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Software coding and Machine construction
🎓 Postgraduate/Undergraduate Research works
📥 Instant Whatsapp/Email Delivery
Related Research
Predicting Disease Outbreaks Using Machine Learning and Data Analysis...
The project topic, "Predicting Disease Outbreaks Using Machine Learning and Data Analysis," focuses on utilizing advanced computational techniques to ...
Implementation of a Real-Time Facial Recognition System using Deep Learning Techniqu...
The project on "Implementation of a Real-Time Facial Recognition System using Deep Learning Techniques" aims to develop a sophisticated system that ca...
Applying Machine Learning for Network Intrusion Detection...
The project topic "Applying Machine Learning for Network Intrusion Detection" focuses on utilizing machine learning algorithms to enhance the detectio...
Analyzing and Improving Machine Learning Model Performance Using Explainable AI Tech...
The project topic "Analyzing and Improving Machine Learning Model Performance Using Explainable AI Techniques" focuses on enhancing the effectiveness ...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project topic "Applying Machine Learning Algorithms for Predicting Stock Market Trends" revolves around the application of cutting-edge machine le...
Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project topic, "Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems," focuses on the integration of machine learn...
Anomaly Detection in Internet of Things (IoT) Networks using Machine Learning Algori...
Anomaly detection in Internet of Things (IoT) networks using machine learning algorithms is a critical research area that aims to enhance the security and effic...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
Anomaly detection in network traffic using machine learning algorithms is a crucial aspect of cybersecurity that aims to identify unusual patterns or behaviors ...
Predictive maintenance using machine learning algorithms...
Predictive maintenance is a proactive maintenance strategy that aims to predict equipment failures before they occur, thereby reducing downtime and maintenance ...