Design and implementation of computer based police investigation system
Table Of Contents
<p> </p><p>Title page i<br>Certification ii<br>Dedication iii<br>Acknowledgement iv<br>Abstract v<br>Organization of work vi<br>Table of contents viii</p><p><b>
Chapter ONE
<br>Introduction 1</b><br>1.1 Statement of the problem 1<br>1.2 purpose of the study 3<br>1.3 Aims and objective 3<br>1.4 Scope of the study 4<br>1.5 Limitations of the study 5<br>1.6 Definition of terms 6</p><p><b>Chapter TWO
</b><br>2.0 Literature review 10</p><p><b>Chapter THREE
<br>3.0 Description and analysis of the existing system 16</b><br>3.1 fact finding methods used 16<br>3.2 Organizational structure 19<br>3.3 Objective of the existing system 21<br>3.4 Input, process, output analysis 21<br>3.5 Information flow diagram 23<br>3.6 Problems of the existing system 24<br>3.7 Justification of the new system 25</p><p><b>Chapter FOUR
<br>4.0 Description of the new system 27</b><br>4.1 output specification and design 27<br>4.2 Input specification and design 29<br>4.3 File design 32<br>4.4 Procedure chart 36<br>4.5 System requirement 38<br><b><br>Chapter FIVE
<br>5.0 Implementation 40</b><br>5.1 program design 40<br>5.2 Pseudo code 44</p><p><b>Chapter six</b><br>6.0 Documentation 51</p><p><b>Chapter seven</b><br>7.0 Recommendation and conclusion 53<br><b>7.1 Reference 56</b></p> <br><p></p>Project Abstract
The world over, it is indisputable that the introduction of computer technology in different facets of life, has virtually transformed and entranced information processing, which is very vital in any organization or parastatals of government. Not only as a means of information processing, the technology has also proved to be the fastest means of information retrieval, which forms the nucleus of this study.
This work tries to x- ray the rate role of the computer in crime investigation as it affects the Nigerian police. Force it looks at ways of improving the information management of the force. This research work will cover the following areas record information retrieval relating to MIS (Management information system), retirement Cretan for officers and crime mapping through a data bank of crime related information.
A detailed design of a computerized approach that will bring the much needed innovation is given. Also included in this work is a proper documentation for the new system design.
Project Overview
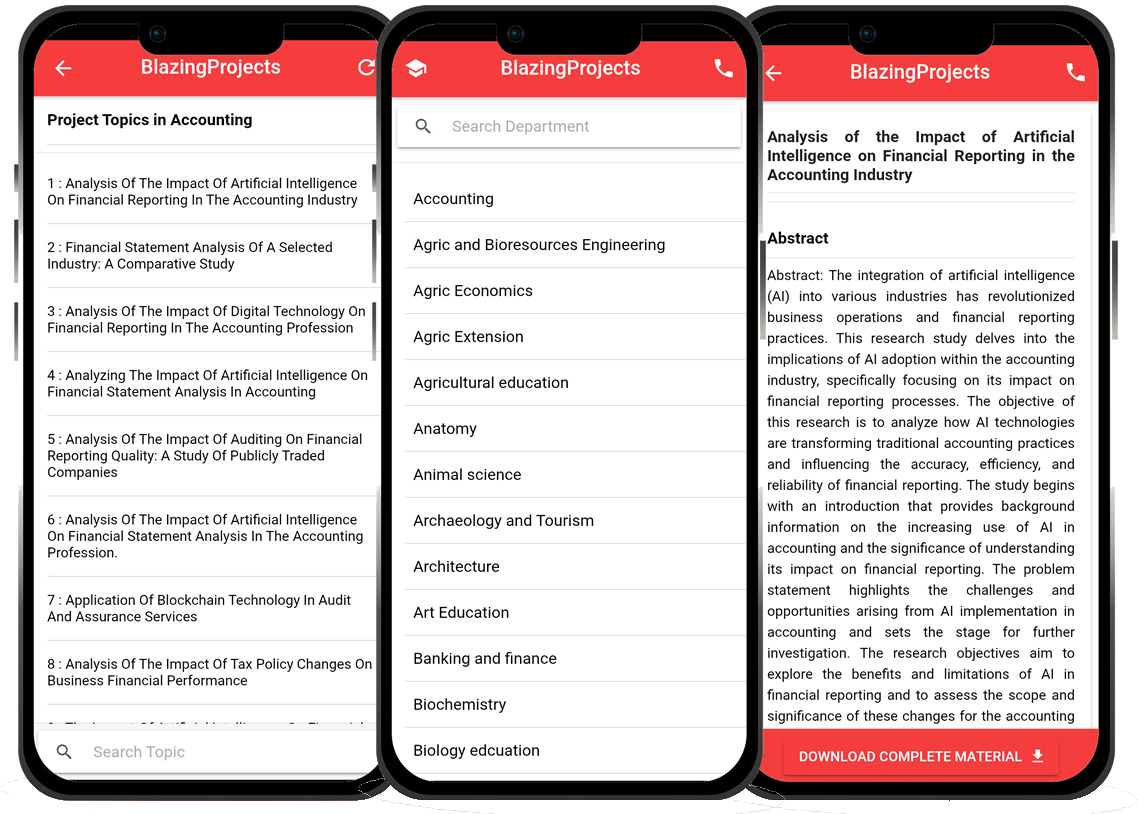
Blazingprojects Mobile App
📚 Over 50,000 Project Materials
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Software coding and Machine construction
🎓 Postgraduate/Undergraduate Research works
📥 Instant Whatsapp/Email Delivery
Related Research
Predicting Disease Outbreaks Using Machine Learning and Data Analysis...
The project topic, "Predicting Disease Outbreaks Using Machine Learning and Data Analysis," focuses on utilizing advanced computational techniques to ...
Implementation of a Real-Time Facial Recognition System using Deep Learning Techniqu...
The project on "Implementation of a Real-Time Facial Recognition System using Deep Learning Techniques" aims to develop a sophisticated system that ca...
Applying Machine Learning for Network Intrusion Detection...
The project topic "Applying Machine Learning for Network Intrusion Detection" focuses on utilizing machine learning algorithms to enhance the detectio...
Analyzing and Improving Machine Learning Model Performance Using Explainable AI Tech...
The project topic "Analyzing and Improving Machine Learning Model Performance Using Explainable AI Techniques" focuses on enhancing the effectiveness ...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project topic "Applying Machine Learning Algorithms for Predicting Stock Market Trends" revolves around the application of cutting-edge machine le...
Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project topic, "Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems," focuses on the integration of machine learn...
Anomaly Detection in Internet of Things (IoT) Networks using Machine Learning Algori...
Anomaly detection in Internet of Things (IoT) networks using machine learning algorithms is a critical research area that aims to enhance the security and effic...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
Anomaly detection in network traffic using machine learning algorithms is a crucial aspect of cybersecurity that aims to identify unusual patterns or behaviors ...
Predictive maintenance using machine learning algorithms...
Predictive maintenance is a proactive maintenance strategy that aims to predict equipment failures before they occur, thereby reducing downtime and maintenance ...