Design and implementation of file encryption and hash system
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of File Encryption2.2 History of File Encryption
2.3 Types of File Encryption Algorithms
2.4 Applications of File Encryption
2.5 Importance of File Encryption
2.6 Challenges in File Encryption
2.7 Comparison of File Encryption Methods
2.8 File Hashing Techniques
2.9 Role of Hash Functions in Data Security
2.10 Implementations of File Encryption and Hash Systems
Chapter THREE
3.1 Research Methodology Overview3.2 Research Design and Approach
3.3 Data Collection Methods
3.4 Sampling Techniques
3.5 Data Analysis Procedures
3.6 Ethical Considerations
3.7 Research Limitations
3.8 Research Validity and Reliability
Chapter FOUR
4.1 Data Analysis and Interpretation4.2 Findings from File Encryption Implementation
4.3 Evaluation of Hashing Algorithms
4.4 Comparison of Encryption and Hashing Techniques
4.5 Security Assessment of the System
4.6 User Feedback and Satisfaction
4.7 Recommendations for System Improvement
4.8 Implications of Findings on Data Security
Chapter FIVE
5.1 Summary of Findings5.2 Conclusion
5.3 Contributions to Knowledge
5.4 Implications for Future Research
5.5 Practical Applications of the Study
5.6 Recommendations for Further Development
5.7 Concluding Remarks
5.8 References
Project Abstract
AbstractIn the modern era of information technology, ensuring the security and integrity of data is paramount. File encryption and hashing are two fundamental techniques used to achieve these goals. This research project focuses on the design and implementation of a file encryption and hash system that provides robust protection for sensitive data. The project involves the development of software that utilizes advanced encryption algorithms to secure files. AES (Advanced Encryption Standard) algorithm is utilized for encrypting the files, ensuring high levels of security. Additionally, a key management system is implemented to securely generate and store encryption keys, enhancing the overall security of the system. In addition to encryption, hashing is employed to verify the integrity of files. The system calculates a hash value for each file using algorithms such as SHA-256 (Secure Hash Algorithm 256-bit). These hash values act as unique fingerprints for each file, allowing users to detect any alterations or tampering with the file contents. The system is designed to be user-friendly, with a simple and intuitive interface for encrypting and decrypting files. Users can easily select files for encryption, set encryption parameters, and generate secure hash values for verification. The system also provides options for securely sharing encrypted files with authorized users, ensuring that data remains protected during transmission. Furthermore, the implementation of the system includes rigorous testing to ensure its reliability and effectiveness. Various test scenarios are conducted to evaluate the performance of the encryption and hashing algorithms, as well as the overall system functionality. Performance metrics such as encryption speed, file integrity verification accuracy, and key management security are assessed to validate the system's capabilities. Overall, the design and implementation of this file encryption and hash system aim to provide a comprehensive solution for securing sensitive data. By combining encryption and hashing techniques with robust key management functionalities, the system offers a reliable and efficient way to protect files from unauthorized access and tampering. This research project contributes to the field of information security by providing a practical and effective tool for safeguarding data in an increasingly digital world.
Project Overview
INTRODUCTION
1.O BACKGROUND OF THE STUDY
The ongoing dilemma of digital age is balancing convenience against security. Security is a system safeguards for protecting information technology against disasters, system failure, and an unauthorized access that can result in damage, loss or exposure. There are several reports of spammers, crawlers and hackers who break into people’s privacy to gain illegal access to their data. This has posed greater challenges on people who use database, transact online, and internet users. Information is a valuable and costly asset that must be presented, controlled and planned just like other valuable assets within an organization. This work is designed to provide a security mechanism using a computerized data encryption system, readable data is altered into unreadable form to prevent unauthorized access. Encryption is able to use powerful mathematical concept to create coded message that is virtually impossible to break. It is easy to encrypt a message on a simple personal computer so that the biggest computer in the world could not decipher without spending for more time on the problem that exists in the life span of the entire universe.
There are two basic forms of encryption; private key encryption and public key encryption, the same secret key is used by the sender and receiver to encrypt and decrypt message. Public key encryption also known as asymmetric key encryption uses two different keys at once, a combination of a private key and public key, the private key is known only to your personal computer, while the public key is given by your computer to any computer that wants to communicate securely with it. To decode an encrypted message, a computer must use the public key, provided by the originating computer, and its own private key.
1.1 STATEMENT OF THE PROBLEM
Security is currently a widespread and growing concern that affects all areas of the society, in the same manner data and information security has become one of the most pressing challenges confronting all kinds of present day organizations owing to their rapid adoption of information technology (IT) in the entirety of their activities. This development has made data and information to a larger extend vulnerable to unauthorized users, spammers, crawlers and hackers who break into people’s and organization’s privacy. This has no doubt posed greater challenges on people who use database, share files and other resources on computer networks.
1.2 AIMS AND OBJECTIVES
The aims and objectives of this work are as follows:
· Reduce stress, time consumption and cost of operation involved in a manual security system.
· Develop a software system that will restrict unauthorized access to data files on systems.
· Suggest security techniques which can create conducive working atmosphere for organizations that are having their data threatened.
· Enhance key sharing mechanism that allows users to share and have access to files security.
1.3 SIGNIFICANCE OF THE STUDY
This study serves as a contribution towards improving information, data and information security on computerized information systems especially for organizations where data is transferred from one point to another. It will contribute in solving the problems of insecurity on both network for individual computers on a network. It also enhances the ability to support customers by providing secured and accurate access to all information. In the same manner, it will benefit those who transact online.
1.4 SCOPE AND LIMITATIONS
This work is only concerned with security of information (encryption and decryption) for firms and individuals. It does not consider the firms policies and other issues.
1.5 JUSTIFICATION OF THE NEW SYSTEM
With regards to existing system, it is important for organization to develop a new system. This system will be designed with security as its watchword. It will be able to check access to the system. It will provide improved system efficiency, the unintentional distortion of data will be avoided and fraudulent practices and defaulters will be checked.
1.6 DEFINITION OF TERMS
· Data: data is the raw fact or observation, typically about physical entity or business transactions. Technically, data is the raw form of information stored as columns and rows in our databases, network servers and personal computers.
· Data security: This is the practice of keeping data protected from corruption and unauthorized access. The focus behind data security is to ensure privacy while protecting personal or corporate data.
· Information: This refers to data that has been processed in such a way to be meaningful to the person who receives it.
· Cryptography: This is the science of scrambling data.
· Encryption: encryption is the conversion of data into a form that cannot be easily understood by an unauthorized people.
· Decryption: Decryption is the process of converting encrypted data back into its original form, so it can be understood.
· Cipher text: this is the encrypted data; it is also called a cipher.
· Decipher text: This is the decrypted data; it is also called a plain text
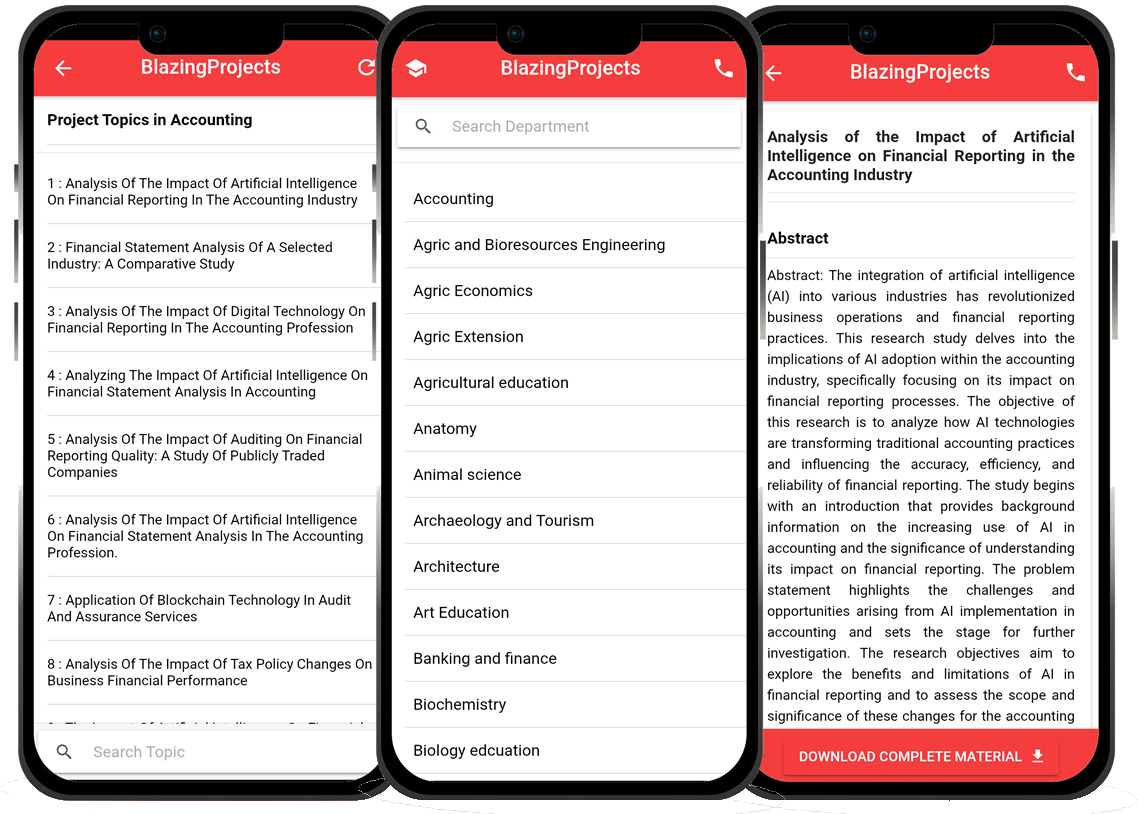
Blazingprojects Mobile App
📚 Over 50,000 Project Materials
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Software coding and Machine construction
🎓 Postgraduate/Undergraduate Research works
📥 Instant Whatsapp/Email Delivery
Related Research
Predicting Disease Outbreaks Using Machine Learning and Data Analysis...
The project topic, "Predicting Disease Outbreaks Using Machine Learning and Data Analysis," focuses on utilizing advanced computational techniques to ...
Implementation of a Real-Time Facial Recognition System using Deep Learning Techniqu...
The project on "Implementation of a Real-Time Facial Recognition System using Deep Learning Techniques" aims to develop a sophisticated system that ca...
Applying Machine Learning for Network Intrusion Detection...
The project topic "Applying Machine Learning for Network Intrusion Detection" focuses on utilizing machine learning algorithms to enhance the detectio...
Analyzing and Improving Machine Learning Model Performance Using Explainable AI Tech...
The project topic "Analyzing and Improving Machine Learning Model Performance Using Explainable AI Techniques" focuses on enhancing the effectiveness ...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project topic "Applying Machine Learning Algorithms for Predicting Stock Market Trends" revolves around the application of cutting-edge machine le...
Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project topic, "Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems," focuses on the integration of machine learn...
Anomaly Detection in Internet of Things (IoT) Networks using Machine Learning Algori...
Anomaly detection in Internet of Things (IoT) networks using machine learning algorithms is a critical research area that aims to enhance the security and effic...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
Anomaly detection in network traffic using machine learning algorithms is a crucial aspect of cybersecurity that aims to identify unusual patterns or behaviors ...
Predictive maintenance using machine learning algorithms...
Predictive maintenance is a proactive maintenance strategy that aims to predict equipment failures before they occur, thereby reducing downtime and maintenance ...