Intrusion detection and prevention system
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Intrusion Detection Systems2.2 Types of Intrusion Detection Systems
2.3 Intrusion Prevention Systems
2.4 Intrusion Detection vs. Intrusion Prevention
2.5 Machine Learning in Intrusion Detection
2.6 Challenges in Intrusion Detection and Prevention Systems
2.7 Best Practices in Intrusion Detection and Prevention
2.8 Case Studies on Intrusion Detection and Prevention Systems
2.9 Emerging Trends in Intrusion Detection and Prevention
2.10 Future Directions in Intrusion Detection and Prevention
Chapter THREE
3.1 Research Methodology Overview3.2 Research Design and Approach
3.3 Data Collection Methods
3.4 Sampling Techniques
3.5 Data Analysis Methods
3.6 Ethical Considerations
3.7 Validity and Reliability
3.8 Limitations of the Research Methodology
Chapter FOUR
4.1 Data Analysis and Interpretation4.2 Overview of Findings
4.3 Analysis of Intrusion Detection System Performance
4.4 Analysis of Intrusion Prevention System Performance
4.5 Comparison of IDS and IPS Effectiveness
4.6 Impact of Machine Learning on Detection and Prevention
4.7 Recommendations for Improvement
4.8 Implications for Practice and Research
Chapter FIVE
5.1 Summary of Findings5.2 Conclusion
5.3 Contributions to Knowledge
5.4 Practical Implications
5.5 Recommendations for Future Research
Project Abstract
AbstractIntrusion detection and prevention systems (IDPS) play a crucial role in safeguarding computer networks and systems from malicious activities. With the increasing complexity and frequency of cyber attacks, there is a growing need for robust IDPS solutions that can effectively detect and mitigate potential threats in real-time. This research focuses on the development and evaluation of an advanced IDPS that combines both signature-based and anomaly-based detection techniques to enhance the overall security posture of a network. The proposed IDPS utilizes signature-based detection to identify known patterns of attacks such as malware signatures and known vulnerabilities. This approach enables the system to quickly recognize and block common threats that have been previously identified. In addition to signature-based detection, the system also incorporates anomaly-based detection to identify abnormal behavior within the network. By establishing baseline behavior patterns for network traffic, the IDPS can detect deviations that may indicate a potential intrusion or security breach. One of the key features of the IDPS is its ability to adapt and learn from new threats over time. Through machine learning algorithms, the system can continuously analyze network traffic patterns and update its detection mechanisms to stay ahead of evolving threats. This adaptive capability enhances the effectiveness of the IDPS in detecting zero-day attacks and previously unknown vulnerabilities. To evaluate the performance of the proposed IDPS, a series of experiments were conducted using a testbed network environment simulating various attack scenarios. The results demonstrate that the IDPS was able to accurately detect and prevent a wide range of attack types, including DDoS attacks, malware infections, and unauthorized access attempts. The system's low false positive rate and high detection accuracy make it a reliable solution for enhancing network security. Overall, this research contributes to the field of intrusion detection and prevention by presenting a comprehensive and adaptive IDPS that can effectively protect networks from cyber threats. By combining signature-based and anomaly-based detection techniques with machine learning capabilities, the proposed system offers a robust defense mechanism against both known and unknown threats. Future work will focus on further enhancing the system's scalability and performance to address the evolving landscape of cybersecurity threats.
Project Overview
INTRODUCTION
An intrusion detection system (IDS) monitors network traffic and monitors for suspicious activity and alert the system or network administrator. In some cases the IDS may also respond to anomalous or malicious traffic by taking action such blocking the user or source IP address from accessing the network. IDS come in a variety of “flavors” and approach the goal of detecting suspicious traffic in different ways. There are network based (NIDS) and host based (HIDS) intrusion detection systems are placed at a strategic point or points within the network to monitor traffic to and from all devices on the network. HIDS host intrusion detection system on the network. HIDS monitors the inbound and outbound pockets from the device only and will alert the user. Intrusion detection, prevention and trace back system are primarily focused on identifying possible incidents, logging information about them, attempting to stop them and reporting them to security administers. Intrusion prevention systems (IPS), also known as intrusion detection and prevention systems (IDPS), are network or system activities for malicious activity. Guide to intrusion detection and prevention systems (IDPS). Computer security resource center, Scarf one [1].
Guide to intrusion detection and prevention systems (IDPS). Computer security resource center, Scarf one [1].
1.1 Statement of the Problem
The following problems were identified in the existing system that necessitated the development of the intrusion detection and prevention system:
- Absence of an intrusion detection and prevention system.
- Insecurity of customer information.
- Inability to prevent intruders from gaining access to sensitive information stored in the computer system.
- Low level of file security.
1.2 Aim and Objectives of Study
The aim of this project is to develop an Intrusion Detection and Prevention System with the following objectives:
(1) To design a system that will encrypt information pertaining to customers to prevent intrusion.
(2) To develop a system that will require an encryption key before bank transaction information can be viewed.
(3) To implement a system that will prevent disclosure of customers’ data to fraudsters by utilizing cipher text.
- Significance of the study
This study is significant in the following ways:
- It will help prevent unauthorized individuals (intruders) from gaining access to the financial information of customers.
- It will help in tightening the security level of the organization.
- The study will reveal how encryption can be applied to prevent intruders from gaining access to customer information.
- The study will serve as a useful reference material to other researchers seeking related information.
1.4 Scope of the Study
This study covers Intrusion Detection, and Prevention System using Gufax micro finance Bank Plc, Ikot Ekpene as a case study. It is limited to the use of cipher text encryption to prevent intruders from gaining access to vital information of customers,
1.5 Organization of the Research
This research work is organized into five chapters, chapter one is concerned with the introduction of the research study and it presents the preliminaries, theoretical background, and statement of the problem, aim and objectives of the study, significance of the study, scope of the study, and organization of the research, Limitation of the study and definition of terms.
Chapter two focuses on the literature review; contribution of other scholars on the subject matter is discussed.
Chapter three contains the system analysis and the design, it presents the research methodology used in development of the system, it analyses the present system to identify the problems and provide information on the merit of the proposed system. The system design is also presented in this chapter.
Chapter four present the system implementation, the choice of programming language used, and system requirement for implementation
Chapter five, this chapter focuses on the summary, conclusion and recommendation are also contained in this chapter based on the study carried out.
Detection is the extraction of particular information from a larger stream of information without specific cooperation from or synchronization with the sender.
Intrusion: It is an illegal act of entering possession of another’s property.
Password: A special code used by user to gain access to the database or a research.
Security: safety, freedom danger.
Files: Is the collection of logically related record.
Prevention: Maintenance performed to stop fault occurring or developing into major detects.
Codes: To write a computer program by putting one system of number, words symbols into another system.
System: a group of interdependent items that interact regularly to perform task
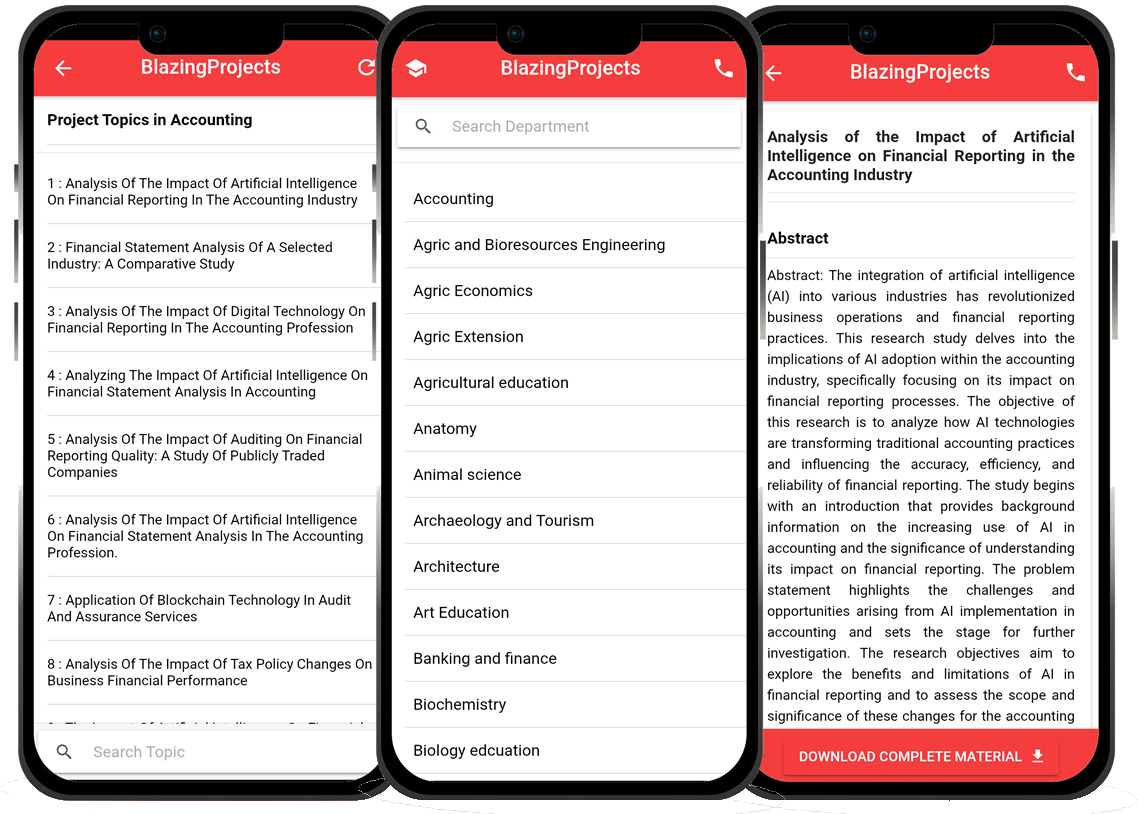
Blazingprojects Mobile App
📚 Over 50,000 Project Materials
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Software coding and Machine construction
🎓 Postgraduate/Undergraduate Research works
📥 Instant Whatsapp/Email Delivery
Related Research
Predicting Disease Outbreaks Using Machine Learning and Data Analysis...
The project topic, "Predicting Disease Outbreaks Using Machine Learning and Data Analysis," focuses on utilizing advanced computational techniques to ...
Implementation of a Real-Time Facial Recognition System using Deep Learning Techniqu...
The project on "Implementation of a Real-Time Facial Recognition System using Deep Learning Techniques" aims to develop a sophisticated system that ca...
Applying Machine Learning for Network Intrusion Detection...
The project topic "Applying Machine Learning for Network Intrusion Detection" focuses on utilizing machine learning algorithms to enhance the detectio...
Analyzing and Improving Machine Learning Model Performance Using Explainable AI Tech...
The project topic "Analyzing and Improving Machine Learning Model Performance Using Explainable AI Techniques" focuses on enhancing the effectiveness ...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project topic "Applying Machine Learning Algorithms for Predicting Stock Market Trends" revolves around the application of cutting-edge machine le...
Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project topic, "Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems," focuses on the integration of machine learn...
Anomaly Detection in Internet of Things (IoT) Networks using Machine Learning Algori...
Anomaly detection in Internet of Things (IoT) networks using machine learning algorithms is a critical research area that aims to enhance the security and effic...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
Anomaly detection in network traffic using machine learning algorithms is a crucial aspect of cybersecurity that aims to identify unusual patterns or behaviors ...
Predictive maintenance using machine learning algorithms...
Predictive maintenance is a proactive maintenance strategy that aims to predict equipment failures before they occur, thereby reducing downtime and maintenance ...