How to prevent computer system infection and compromise using trojan tool and process
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Computer System Infections2.2 Types of Computer System Infections
2.3 Trojan Tools and Processes
2.4 Common Entry Points for Infections
2.5 Effects of Computer System Infections
2.6 Strategies for Preventing System Infections
2.7 Importance of Regular Updates and Patches
2.8 Role of Antivirus and Firewall Software
2.9 User Awareness and Training
2.10 Case Studies on Successful Prevention Methods
Chapter THREE
3.1 Research Design and Approach3.2 Sampling Techniques
3.3 Data Collection Methods
3.4 Data Analysis Tools
3.5 Ethical Considerations
3.6 Validity and Reliability
3.7 Pilot Study
3.8 Limitations of the Research
Chapter FOUR
4.1 Analysis of Research Findings4.2 Comparison of Prevention Methods
4.3 Effectiveness of Trojan Tools
4.4 Impact of User Training on Prevention
4.5 Case Studies Analysis
4.6 Recommendations for Future Research
4.7 Practical Implications
4.8 Policy Recommendations
Chapter FIVE
5.1 Summary of Findings5.2 Conclusion
5.3 Contributions to the Field
5.4 Implications for Practice
5.5 Recommendations for Action
5.6 Areas for Future Research
Project Abstract
AbstractComputer system infections and compromises through Trojan tools and processes pose a significant threat to individuals and organizations alike. This research project aims to explore effective strategies for preventing such security breaches. The study delves into the various methods used by cybercriminals to deploy Trojans and compromise computer systems, highlighting the importance of understanding the tactics employed by malicious actors. The research emphasizes the crucial role of user awareness and education in preventing Trojan infections. By educating users on safe browsing habits, email security best practices, and the risks associated with downloading unknown files, organizations can significantly reduce the likelihood of falling victim to Trojan attacks. Additionally, implementing robust security measures such as firewalls, antivirus software, and intrusion detection systems can help detect and block Trojan activity. Furthermore, the study investigates the importance of regularly updating software and operating systems to patch vulnerabilities that could be exploited by Trojans. By staying current with security patches and updates, organizations can strengthen their defenses against potential breaches. The research also explores the significance of conducting regular security audits and penetration testing to identify and address any weaknesses in the system that could be leveraged by cybercriminals. Moreover, the project examines the role of endpoint security solutions in preventing Trojan infections. Endpoint security tools such as endpoint detection and response (EDR) systems can help detect and respond to suspicious activities on endpoints, providing an additional layer of defense against Trojan attacks. By deploying endpoint security solutions across all devices within an organization, businesses can enhance their overall security posture and mitigate the risk of compromise. In conclusion, this research project underscores the importance of a multi-faceted approach to preventing computer system infections and compromises through Trojan tools and processes. By combining user education, robust security measures, regular software updates, security audits, and endpoint security solutions, organizations can effectively defend against Trojan attacks and safeguard their sensitive data and systems. Ultimately, proactive measures and a comprehensive security strategy are essential in mitigating the risks posed by Trojan tools and processes in today's digital landscape.
Project Overview
INTRODUCTION
1.1 BACKGROUND TO THE STUDY
Computer system infection, also known as malicious code, refers to a program that is covertly inserted into another program with the intent to destroy data, run destructive or intrusive programs, or otherwise compromise the confidentiality, integrity, or availability of the victim’s data, applications, or operating system (Higgins, 2010). Computer system infection is the most common external threat to most hosts, causing widespread damage and disruption and necessitating extensive recovery efforts within most organizations. Organizations also face similar threats from a few forms of non-malware threats that are often associated with computer system infection. One of these forms that has become commonplace is phishing, which is using deceptive computer-based means to trick individuals into disclosing sensitive information. Organizations should plan and implement an approach to computer system infection incident prevention based on the attack vectors that are most likely to be used currently and in the near future. Because the effectiveness of prevention techniques may vary depending on the environment (i.e., a technique that works well in a managed environment might be ineffective in a non-managed environment), organizations should choose preventive methods that are well-suited to their environment and hosts. An organization’s approach to computer system infection incident prevention should incorporate policy considerations, awareness programs for users and information technology (IT) staff, vulnerability and threat mitigation efforts, and defensive architecture considerations (Higgins, 2010).
An organization’s policy statements should be used as the basis for additional malware prevention efforts, such as user and IT staff awareness, vulnerability mitigation, threat mitigation, and defensive architecture. If an organization does not state consider system infection prevention considerations clearly in its policies, it is unlikely to perform infection prevention activities consistently and effectively throughout the organization (Goodin, 2007). Computer infection preventionrelated policy should be as general as possible to provide flexibility in policy implementation and to reduce the need for frequent policy updates, but should also be specific enough to make the intent and scope of the policy clear. Computer system preventionrelated policy should include provisions related to remote workers“both those using hosts controlled by the organization and those using hosts outside of the organization’s control (e.g., contractor computers, employees’ home computers, business partners’ computers, mobile devices).
Trojan has been building tools that you can trust for more than a century. It’s worthy to note that there’s no substitute for quality. These tools are used has antivirus. Antivirus software was originally developed to detect and remove computer viruses, hence the name. However, with the proliferation of other kinds of computer infection, antivirus software started to provide protection from other computer threats. In particular, modern antivirus software can protect from: malicious Browser Helper Objects (BHOs), browser hijackers, ransomware, keyloggers, backdoors, rootkits, trojan horses, worms, malicious LSPs, dialers, fraudtools, adware and spyware. Some products also include protection from other computer threats, such as infected and malicious URLs, spam, scam and phishing attacks, online identity (privacy), online banking attacks, social engineering techniques, Advanced Persistent Threat (APT) and botnet DDoS attacks (Harley, 2011).
Anti-virus programs are not always effective against new viruses, even those that use non-signature-based methods that should detect new viruses. The reason for this is that the virus designers test their new viruses on the major anti-virus applications to make sure that they are not detected before releasing them into the wild
1.2 STATEMENT OF THE PROBLEM
Computer infection incident containment has two major components: stopping the spread of infection and preventing further damage to hosts. Nearly every infection incident requires containment actions. In addressing an incident, it is important for an organization to decide which methods of containment to employ initially, early in the response. Organizations should have strategies and procedures in place for making containment-related decisions that reflect the level of risk acceptable to the organization. Containment strategies should support incident handlers in selecting the appropriate combination of containment methods based on the characteristics of a particular situation. This study is examining the method of preventing computer system infection and compromise using Trojan tool and process.
1.3 OBJECTIVES OF THE STUDY
The following are the objectives of this study:
- To examine the methods of preventing computer system infection.
- To determine the capability of Trojan tool and process in preventing computer system infection.
- To identify the consequences of computer system infection.
1.4 RESEARCH QUESTIONS
- What are the methods of preventing computer system infection?
- What is the capability of Trojan tool and process in preventing computer system infection?
- What are the consequences of computer system infection?
1.6 SIGNIFICANCE OF THE STUDY
The following are the significance of this study:
- The outcome of this study will educate computer users and the general public on the issues of computer system infection. It will also educate on how to prevent computer system infection and compromise using Trojan tools and process.
- This research will be a contribution to the body of literature in the area of the effect of personality trait on student’s academic performance, thereby constituting the empirical literature for future research in the subject area.
1.7 SCOPE/LIMITATIONS OF THE STUDY
This study will cover the method of preventing computer system infection using Trojan tools and process.
LIMITATION OF STUDY
Financial constraint– Insufficient fund tends to impede the efficiency of the researcher in sourcing for the relevant materials, literature or information and in the process of data collection (internet, questionnaire and interview).
Time constraint– The researcher will simultaneously engage in this study with other academic work. This consequently will cut down on the time devoted for the research work
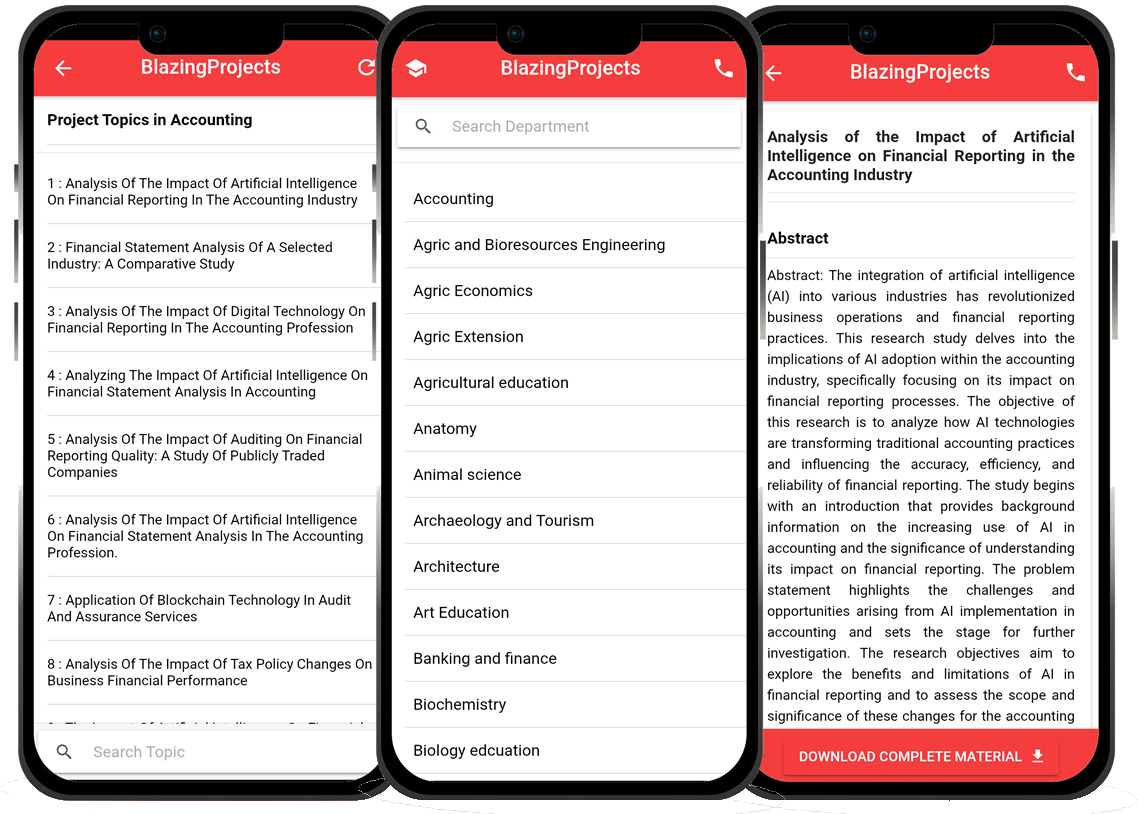
Blazingprojects Mobile App
📚 Over 50,000 Project Materials
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Software coding and Machine construction
🎓 Postgraduate/Undergraduate Research works
📥 Instant Whatsapp/Email Delivery
Related Research
Predicting Disease Outbreaks Using Machine Learning and Data Analysis...
The project topic, "Predicting Disease Outbreaks Using Machine Learning and Data Analysis," focuses on utilizing advanced computational techniques to ...
Implementation of a Real-Time Facial Recognition System using Deep Learning Techniqu...
The project on "Implementation of a Real-Time Facial Recognition System using Deep Learning Techniques" aims to develop a sophisticated system that ca...
Applying Machine Learning for Network Intrusion Detection...
The project topic "Applying Machine Learning for Network Intrusion Detection" focuses on utilizing machine learning algorithms to enhance the detectio...
Analyzing and Improving Machine Learning Model Performance Using Explainable AI Tech...
The project topic "Analyzing and Improving Machine Learning Model Performance Using Explainable AI Techniques" focuses on enhancing the effectiveness ...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project topic "Applying Machine Learning Algorithms for Predicting Stock Market Trends" revolves around the application of cutting-edge machine le...
Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project topic, "Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems," focuses on the integration of machine learn...
Anomaly Detection in Internet of Things (IoT) Networks using Machine Learning Algori...
Anomaly detection in Internet of Things (IoT) networks using machine learning algorithms is a critical research area that aims to enhance the security and effic...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
Anomaly detection in network traffic using machine learning algorithms is a crucial aspect of cybersecurity that aims to identify unusual patterns or behaviors ...
Predictive maintenance using machine learning algorithms...
Predictive maintenance is a proactive maintenance strategy that aims to predict equipment failures before they occur, thereby reducing downtime and maintenance ...