Design and development of internet security package
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Internet Security2.2 Historical Development of Internet Security
2.3 Types of Internet Security Threats
2.4 Strategies for Internet Security
2.5 Importance of Internet Security
2.6 Technologies Used in Internet Security
2.7 Current Trends in Internet Security
2.8 Challenges in Internet Security
2.9 Best Practices in Internet Security
2.10 Future of Internet Security
Chapter THREE
3.1 Research Design3.2 Research Methods
3.3 Data Collection Techniques
3.4 Sampling Methods
3.5 Data Analysis Procedures
3.6 Ethical Considerations
3.7 Research Limitations
3.8 Research Validity and Reliability
Chapter FOUR
4.1 Overview of Research Findings4.2 Analysis of Data
4.3 Comparison of Results with Literature
4.4 Interpretation of Findings
4.5 Discussion on Key Findings
4.6 Implications of Findings
4.7 Recommendations for Practice
4.8 Suggestions for Future Research
Chapter FIVE
5.1 Conclusion and Summary5.2 Summary of Findings
5.3 Contributions to Knowledge
5.4 Practical Implications
5.5 Recommendations for Action
5.6 Areas for Future Research
Project Abstract
AbstractThe design and development of an internet security package is a crucial undertaking in the modern digital landscape. With the increasing prevalence of cyber threats such as malware, phishing attacks, and data breaches, ensuring the security of internet-connected devices and networks has become paramount. This research project aims to create a comprehensive internet security package that provides robust protection against a wide range of cyber threats. The internet security package will incorporate various security features, including firewall protection, antivirus software, intrusion detection systems, and encryption tools. By integrating these different components into a unified package, users can benefit from a multi-layered approach to security that addresses both known and emerging threats. One key aspect of the internet security package is its user-friendly interface, which is designed to be intuitive and easy to use for individuals with varying levels of technical expertise. This accessibility is essential in ensuring that users can effectively manage their security settings and respond to potential threats in a timely manner. In addition to providing real-time protection against cyber threats, the internet security package will also include features for regular system scans, software updates, and vulnerability assessments. These proactive measures are essential for maintaining the integrity and security of internet-connected devices over time. Furthermore, the internet security package will be designed to be customizable, allowing users to configure security settings based on their specific needs and preferences. This flexibility ensures that users can tailor their security measures to align with their unique usage patterns and risk profiles. To develop the internet security package, a combination of programming languages, security protocols, and encryption algorithms will be utilized. Additionally, extensive testing and validation processes will be conducted to ensure the effectiveness and reliability of the security package in real-world scenarios. Overall, the design and development of an internet security package represent a critical step in safeguarding the confidentiality, integrity, and availability of digital information in an increasingly interconnected world. By creating a comprehensive security solution that combines multiple layers of protection with user-friendly features and proactive measures, this research project aims to enhance the overall security posture of internet users and organizations.
Project Overview
11 BACKGROUND OF THE STUDY
The Internet has been described as the most revoluntary communication development of last century It has changed everything about every type of business and there seems no end in sight to the advantages this phenomenon can bring to this enhancement of business communications The Internet is a system for providing communication links between computers via local companies referred to as Internet of computer networks that is changing the way organizations and individuals communicates and do business
However, the major drawback is the security risks associated with it The Internet suffers from a significant and widespread security problems Perhaps, most important of all reason adduced for the poor security facilities on the internet may be the fact that was not designed to every secure: open access for the purpose of research was the prime motivation for the internet at the time of its conception Other factors responsible for the security lapse of the internet which is based on the TCP/IP (Transmission Control Protocol/Internet Protocol) suite of protocol A number of TCP/IP (Transmission Control Protocol/ Internet Protocol) suites of protocols A number of TCP/IP services are not secured and compromised by knowledgeable hackers A number of security problems can be remedied or reduced through the use of this software and control for host security
12 STATEMENT OF PROBLEMS
Some of the problems with the internet security are as a result of inherent vulnerabilities in the services (and the protocols that the services implement), while others are as a result of host configuration and access controls that are poorly implemental or overly complex to administer Additionally, the role and importance of system management is often short-changed in job description resulting in many administrators begin at best, part-time and poorly prepared
Further more, the unavailability of experts who will carry the job for the people Also the cost at which people or individuals will undergo before acquiring one will also arise to be a problem
13 OBJECTIVES OF THE PROJECT
The objective of this research work is to develop a client billing software program with modification of existing software and eliminating the entire obstacle in previous version of the numerous existing clients billing software program Apart from producing an enhancement,
It will also:
i prepare daily account of all transaction with clients
ii Produce analyzed report for decision making
iii Provide security to enhance system lock when credit expires
iv Automatically generate numbers as ID’S and allocate time and payments by clients
v Enable the system within the network to identify user with particular name and password
14 SIGNIFICANCE OF THE PROJECT
Like any other application development the significance of this project is to make internet café business much more profitable to the investors
An internet café without effective security will gradually die because of pester and cashier stall time spend by clients
This software is intended to stop the death of internet café’s with attendant un employment in the space This will be facilitated by the development of automated technique ie café billing to check time automatically
15 SCOPE OF STUDY
This project work or study is aimed at designing and developing a time billing software for the Access Point Communication Limited
Furthermore, it is also aimed at saving the management of the access point communication limited the trouble and difficulties in running an internet café manually
16 LIMITATION
The main problem encountered or the constraints in the course of this research were with the initial difficulty in grasping the knowledge of the field, which was quite alien to the researcher Though this was overcame within a short period of time
Also, the obtaining of accurate and complete information from the case study (Access Point Communication Limited) was somewhat inhibited The researcher had to do some independent investigations and internet browsing to ensure that relevant information was used
Finally, the issue of time can not be forgotten This was a very limited time to carry out the research or the project and also limited time to produce the project work
17 DEFINITION OF TERMS
INTERNET: this is an act linking several computers in the world in a wide area network
E-MAIL: the term electronic mail is used to describe various system of sending data or message electronically via the telephone Network or other data network, through a central computer without the need to post letters
SECURITY: this is an act of safeguarding a file or a document in order to allow unauthorized access
FLOWCHART: This is the diagrammatic representation of the program components using standard symbols
HARDWARE: this is the physical part of a computer system
SOFTWARE: This is the program that controls the computer operation
DATABASE: A collection of interrelated data stored with controlled redundancy to serve one or more application
MICRO SOFT VISUAL BASIC: This is software which allows you to develop your own software
WWW: – This stands for World Wide Web which consists of the different website which you can visit
NEWS GROUP: These are meeting please for people discussing special topic
NETWORK SERVERS: These are devices used to manage how the various resources on the network are shared
HACKING: A hacker is people who attempt to invade the privacy of a system Hackers are normally skilled programmers
METHODOLOGY: A methodology is a collection of procedure techniques, tools and documentation aids which will help the system developer in their effort to implement a new information system, Abdul j I
ONLINE: This is the direct connection to the computers through the internet and under the influence of the computer CPU
OFFLINE: This is the process of the computer not connected to the internet
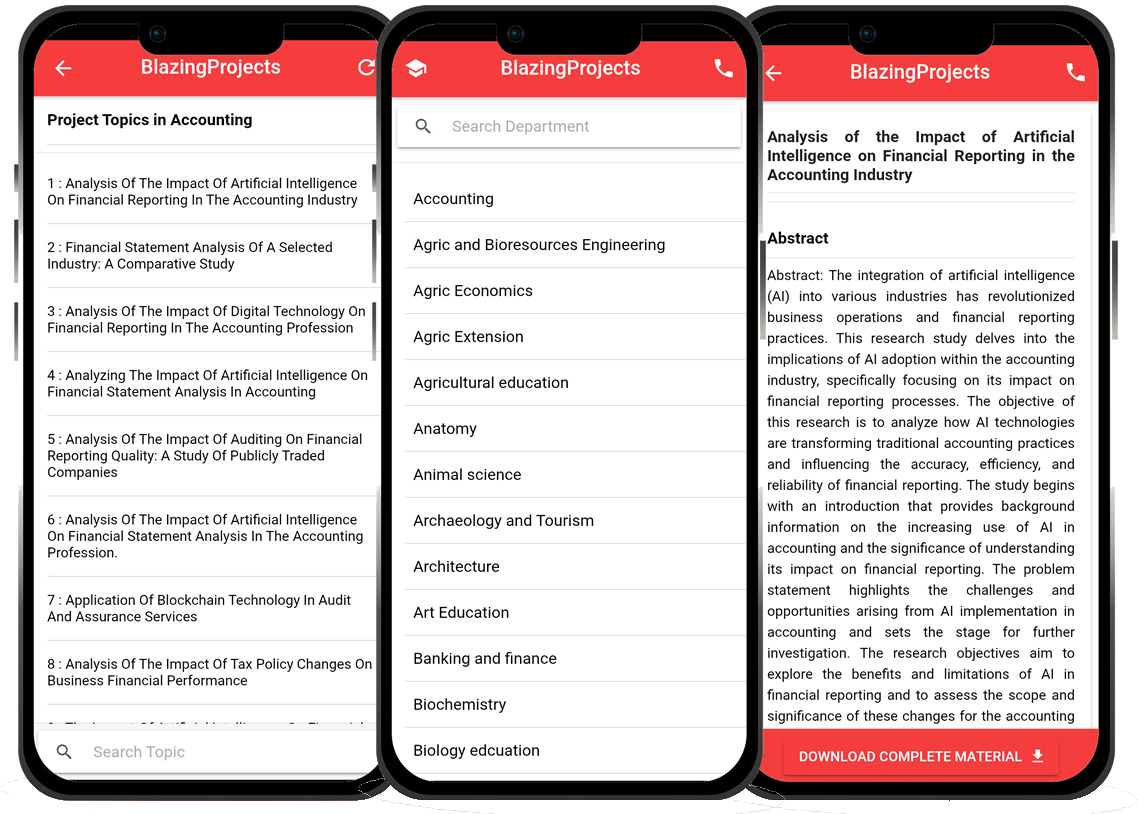
Blazingprojects Mobile App
📚 Over 50,000 Project Materials
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Software coding and Machine construction
🎓 Postgraduate/Undergraduate Research works
📥 Instant Whatsapp/Email Delivery
Related Research
Predicting Disease Outbreaks Using Machine Learning and Data Analysis...
The project topic, "Predicting Disease Outbreaks Using Machine Learning and Data Analysis," focuses on utilizing advanced computational techniques to ...
Implementation of a Real-Time Facial Recognition System using Deep Learning Techniqu...
The project on "Implementation of a Real-Time Facial Recognition System using Deep Learning Techniques" aims to develop a sophisticated system that ca...
Applying Machine Learning for Network Intrusion Detection...
The project topic "Applying Machine Learning for Network Intrusion Detection" focuses on utilizing machine learning algorithms to enhance the detectio...
Analyzing and Improving Machine Learning Model Performance Using Explainable AI Tech...
The project topic "Analyzing and Improving Machine Learning Model Performance Using Explainable AI Techniques" focuses on enhancing the effectiveness ...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project topic "Applying Machine Learning Algorithms for Predicting Stock Market Trends" revolves around the application of cutting-edge machine le...
Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project topic, "Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems," focuses on the integration of machine learn...
Anomaly Detection in Internet of Things (IoT) Networks using Machine Learning Algori...
Anomaly detection in Internet of Things (IoT) networks using machine learning algorithms is a critical research area that aims to enhance the security and effic...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
Anomaly detection in network traffic using machine learning algorithms is a crucial aspect of cybersecurity that aims to identify unusual patterns or behaviors ...
Predictive maintenance using machine learning algorithms...
Predictive maintenance is a proactive maintenance strategy that aims to predict equipment failures before they occur, thereby reducing downtime and maintenance ...