Design and implementation of a crypto-stego security system
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Cryptography2.2 History of Steganography
2.3 Principles of Crypto-Stego Systems
2.4 Types of Encryption Algorithms
2.5 Steganographic Techniques
2.6 Challenges in Crypto-Stego Security
2.7 Applications of Crypto-Stego Systems
2.8 Comparison of Crypto-Stego Tools
2.9 Future Trends in Crypto-Stego Technology
2.10 Case Studies on Crypto-Stego Implementations
Chapter THREE
3.1 Research Design3.2 Data Collection Methods
3.3 Sampling Techniques
3.4 Data Analysis Procedures
3.5 Research Ethics
3.6 Instrumentation and Tools
3.7 Validity and Reliability
3.8 Limitations of the Methodology
Chapter FOUR
4.1 Overview of Data Analysis4.2 Presentation of Findings
4.3 Analysis of Results
4.4 Comparison with Existing Literature
4.5 Interpretation of Data
4.6 Identification of Patterns and Trends
4.7 Discussion on Research Questions
4.8 Implications for Practice and Future Research
Chapter FIVE
5.1 Summary of Findings5.2 Conclusion
5.3 Contribution to Knowledge
5.4 Recommendations for Implementation
5.5 Areas for Future Research
5.6 Reflection on the Research Process
5.7 Practical Applications of the Study
5.8 Conclusion Statement
Thesis Abstract
AbstractThis research focuses on the design and implementation of a crypto-stego security system that combines cryptography and steganography techniques to enhance data security and confidentiality. The system aims to provide a robust and efficient solution for securing sensitive information in various applications, including communication networks, cloud storage, and digital transactions. The proposed system leverages cryptographic algorithms for data encryption to protect the content from unauthorized access. Advanced encryption standards such as AES and RSA are employed to ensure secure communication and storage of data. Additionally, the system integrates steganography techniques to hide encrypted data within innocuous cover media, such as images or audio files, to further strengthen the security of the information. The design of the crypto-stego security system involves the development of encryption and decryption modules for securing data and embedding it into cover media using steganography techniques. The encryption module utilizes strong encryption algorithms to encode the data before embedding it into the cover media. On the other hand, the decryption module extracts and decrypts the hidden data from the cover media to retrieve the original information. To implement the system, software tools and programming languages like Python and Java are utilized to build the encryption, decryption, and steganography modules. The system architecture includes components for data encryption, steganography embedding, cover media generation, and data extraction. Proper key management and authentication mechanisms are integrated into the system to ensure secure data handling and access control. The performance evaluation of the crypto-stego security system involves testing its effectiveness in terms of data security, embedding capacity, and computational overhead. Various metrics such as encryption strength, payload capacity, and processing time are measured to assess the system's security and efficiency. The experimental results demonstrate the system's ability to securely embed and extract data from cover media while maintaining a balance between security and performance. Overall, the design and implementation of the crypto-stego security system provide a comprehensive solution for safeguarding sensitive information through a combination of cryptography and steganography techniques. The system offers a practical approach to enhance data security and confidentiality in modern communication and information systems, contributing to the advancement of secure data transmission and storage technologies.
Thesis Overview
This research work has led to the development of a data encryption system that organizations and individuals can use for secure data communication, and to keep private/secret information as confidential as possible. The Waterfall model was used in the analysis of the existing systems and identification of lapses/weaknesses. These weaknesses were corrected/checked by the new system developed using Python. The new system provides security to data/information by encrypting the message and then hides/embeds the encrypted form of the message in any type of image file. The importance of the study of information security cannot be over emphasized in our society
today as it helps to save a lot of situation concerning information confidentiality, integrity, and it’s availability for only the intended person(s), and further help save information from attackers who may want to use the information to achieve some malicious intent, for probably selfish interests. The proposed system achieves this by encrypting a secret message using AES algorithm and hiding it in an image file using the LSB algorithm making it possible to maintain the integrity of the secret message.
In this project we have presented a new system for the combination of cryptography and Steganography using two keys (user password and unique number) which could be proven a highly secured method for data communication. Cryptography, especially when combined with steganography, is a powerful tool which enables people to communicate without possible eavesdroppers even knowing there is a form of communication in the first place. The main advantage of this Crypto-Stego System is that the method used for encryption, AES, is very secure and the LSB transformation Steganography techniques are very hard to detect. This proposed method can also withstand different attacks and thus a very strong and robust method of data security can be obtained.
BACKGROUND OF STUDY
In the present world of communication, one of the necessary requirements to prevent data theft is securing the information. Security has become a critical feature for thriving networks and in military alike. Cryptography and Steganography are well known and widely used techniques that manipulate information (messages) in order to cipher or hide their existence. These techniques have many applications in computer science and other related fields: they are used to protect military messages, E-mails, credit card information, corporate data, personal files, etc. This protection is done or carried out by first generally encrypting the data, then hiding it so as to only be discovered for whom it is meant or intended for. Before the modern era, cryptography was concerned solely with message confidentiality (.i.e., encryption “ conversion of messages from a comprehensible form into an incomprehensible one, and back again at the other end), rendering it unreadable by interceptors or eavesdroppers without the secret knowledge which is the key needed for decrypting the message. In recent decades, the field has expanded beyond confidentiality concerns to include techniques for message integrity checking, sender/receiver identity authentication, digital signatures, interactive proofs, and secure computation, amongst others. Encryption attempts to ensure secrecy in communications, such as those of spies, military leaders, diplomats etc.
Steganography (“ hiding the existence of a message so as to keep it confidential) was also first developed in ancient times. An early example, from Herodotus (- a Greek historian), concealed a message a tattoo on a slave’s shaved head under the regrown hair. In modern terms, Steganography is usually implemented computationally, where cover works such as text files, images, audio files, and video files are altered in such a way that a secret message can be embedded within them. Although Steganography techniques are very similar to that of digital watermarking, one big distinction must be highlighted between the two. In digital watermarking, the focus is on ensuring that nobody can remove or alter the content of the watermarked data, even though it might be plainly obvious that it exists. Steganography on the other hand, focuses on making it extremely difficult to tell that a secret message exists at all. If an unauthorized third party is able to say with high confidence that a file contains a secret message, then steganography has failed
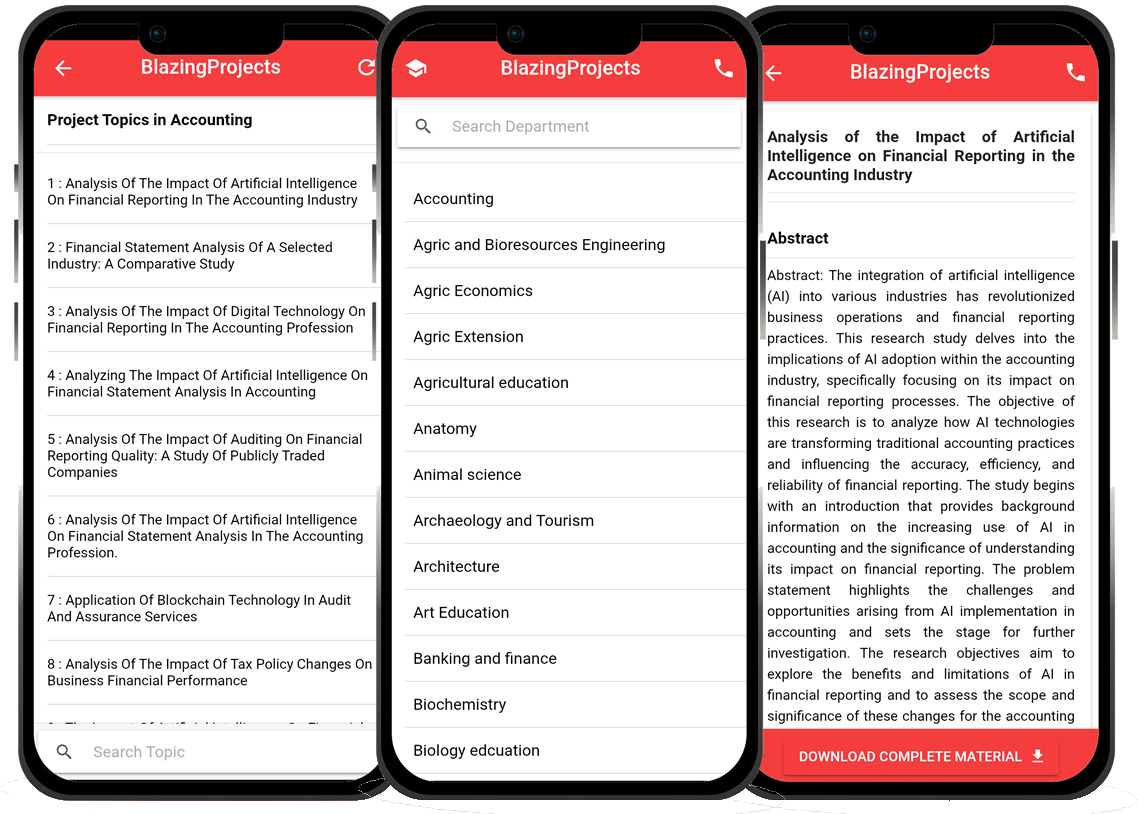
Blazingprojects Mobile App
📚 Over 50,000 Research Thesis
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Thesis-to-Journal Publication
🎓 Undergraduate/Postgraduate Thesis
📥 Instant Whatsapp/Email Delivery
Related Research
Applying Machine Learning Techniques to Detect Financial Fraud in Online Transaction...
The project titled "Applying Machine Learning Techniques to Detect Financial Fraud in Online Transactions" aims to address the critical issue of detec...
Anomaly Detection in IoT Networks Using Machine Learning Algorithms...
The project titled "Anomaly Detection in IoT Networks Using Machine Learning Algorithms" focuses on addressing the critical challenge of detecting ano...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project titled "Applying Machine Learning Algorithms for Predicting Stock Market Trends" aims to explore the application of machine learning algor...
Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data...
The project titled "Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data" focuses on utilizing machine learning algorithms...
Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project titled "Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems" focuses on leveraging machine learning techniques ...
Implementation of a Machine Learning Algorithm for Predicting Stock Prices...
The project, "Implementation of a Machine Learning Algorithm for Predicting Stock Prices," aims to leverage the power of machine learning techniques t...
Development of an Intelligent Traffic Management System using Machine Learning Algor...
The project titled "Development of an Intelligent Traffic Management System using Machine Learning Algorithms" aims to revolutionize the traditional t...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
No response received....
Applying Machine Learning for Intrusion Detection in IoT Networks...
The project titled "Applying Machine Learning for Intrusion Detection in IoT Networks" aims to address the increasing cybersecurity threats targeting ...