ETHICAL HACKING AND CYBER SECURITY IN NIGERIAN TELECOMMUNICATION INDUSTRY: ISSUES AND SOLUTIONS
Table Of Contents
Title page — – – – – – – – – – – i
Declaration — – – – – – – – – – -ii
Approval page — – – – – – – – – – -iii
Dedication — – – – – – – – – – -iv
Acknowledgement — – – – – – – – – -v
Table of content — – – – – – – – – -vi Abstract — – – – – – – – – – – -vii
Thesis Abstract
AbstractEthical hacking and cyber security are critical components in ensuring the protection of sensitive information and infrastructure in the Nigerian telecommunication industry. This research aims to investigate the current issues and challenges faced in this sector regarding cyber security and ethical hacking practices, as well as propose effective solutions to mitigate these risks. The Nigerian telecommunication industry has experienced rapid growth in recent years, leading to an increased reliance on digital technologies and communication networks. However, this growth has also made the industry a prime target for cyber attacks and security breaches. The interconnected nature of telecommunication networks and the vast amount of data transmitted through these networks make them vulnerable to various cyber threats. One of the main issues identified in the industry is the lack of adequate cyber security measures and ethical hacking practices. Many telecommunication companies in Nigeria do not prioritize cyber security, leading to vulnerabilities that can be exploited by malicious actors. Additionally, the shortage of skilled professionals in the field of ethical hacking and cyber security further exacerbates these challenges. To address these issues, this research proposes several solutions. Firstly, there is a need for telecommunication companies to invest in robust cyber security measures, such as firewalls, encryption, and intrusion detection systems. Additionally, regular security audits and penetration testing should be conducted to identify and rectify vulnerabilities in the network. Furthermore, training programs and workshops should be organized to enhance the skills of professionals in ethical hacking and cyber security. By investing in training and development, companies can build a competent workforce capable of defending against sophisticated cyber threats. Moreover, collaboration between telecommunication companies, government agencies, and regulatory bodies is essential to establish industry-wide standards and best practices for cyber security. Information sharing and coordination can help in the early detection and mitigation of cyber attacks, ultimately safeguarding the integrity of telecommunication networks in Nigeria. In conclusion, ethical hacking and cyber security are indispensable in the Nigerian telecommunication industry to protect against evolving cyber threats. By implementing the proposed solutions and fostering a culture of security awareness, telecommunication companies can enhance their resilience against cyber attacks and ensure the confidentiality, integrity, and availability of their services.
Thesis Overview
INTRODUCTION
1.1 BACKGROUND TO THE STUDY
Cyber security through ethical hacking plays an important role in the ongoing development of telecommunication industry, as well as Internet services (Odinma, 2010). Enhancing cyber security and protecting critical information infrastructures are essential to each nation’s security and economic well-being (Odinma, 2010). Making the Internet safer (and protecting Internet users) has become integral to the development of new services as well as government policy. An ethical hacker is a computer and networking expert who systematically attempts to penetrate a computer system or telecommunication network on behalf of its owners for the purpose of finding security vulnerabilities that a malicious hacker could potentially exploit (Okonigene & Adekanle, 2009). Ethical hackers use the same methods and techniques to test and bypass a system's defenses as their less-principled counterparts, but rather than taking advantage of any vulnerabilities found, they document them and provide actionable advice on how to fix them so the organization can improve its overall security (Laura, 1995).
The purpose of ethical hacking is to evaluate the security of a network or system's infrastructure. It entails finding and attempting to exploit any vulnerabilities to determine whether unauthorized access or other malicious activities are possible. Vulnerabilities tend to be found in poor or improper system configuration, known and unknown hardware or software flaws, and operational weaknesses in process or technical countermeasures. One of the first examples of ethical hacking occurred in the 1970s, when the United States government used groups of experts called "red teams" to hack its own computer systems (Laura, 1995). It has become a sizable sub-industry within the information security market and has expanded to also cover the physical and human elements of an organization's defenses.
A successful test doesn't necessarily mean a network or system is 100% secure, but it should be able to withstand automated attacks and unskilled hackers. Deterring cybercrime is an integral component of a national cybersecurity and critical information infrastructure protection strategy. In particular, this includes the adoption of appropriate legislation against the misuse of ICTs for criminal or other purposes and activities intended to affect the integrity of national critical infrastructures (Adebusuyi, 2008). At the national level, this is a shared responsibility requiring coordinated action related to prevention, preparation, response and recovery from incidents on the part of government authorities, the private sector and citizens. The exceptional outbreak of cyber-crime in Nigeria in recent times was quite alarming, and the negative impact on the socio-economy of the country is highly disturbing.Over the past twenty years, immoral cyberspace users have continued to use the internet to commit crimes; this has evoked mixed feelings of admiration and fear in the general populace along with a growing unease about the state of cyber and personal security (Oliver, 2010). This phenomenon has seen sophisticated and extraordinary increase recently and has called for quick response in providing laws that would protect the cyber space and its users. The first recorded cyber murder was committed in the United States seven years ago.
According to the Indian Express, January 2002, an underworld don in a hospital was to undergo a minor surgery. His rival went ahead to hire a computer expert who altered his prescriptions through hacking the hospital’s computer system. He was administered the altered prescription by an innocent nurse, this resulted in the death of the patient. Statistically, all over the world, there has been a form of cyber-crime committed every day since 2006. Prior to the year 2001, the phenomenon of cyber-crime was not globally associated with Nigeria. This resonates with the fact that in Nigeria we came into realization of the full potential of the internet right about that time. Since then, however, the country has acquired a world-wide notoriety in criminal activities, especially financial scams, facilitated through the use of the Telecommunication facilities.
Nigerian cyber criminals are daily devising new ways of perpetrating this form of crime and the existing methods of tracking these criminals are no longer suitable for to deal with their new tricks (Adebusuyi, 2008). The victims as well show increasing naivety and gullibility at the prospects incited by these fraudsters. This paper seeks to give an overview of ethical hacking and cyber-security in Nigerian telecommunication industry, outline some challenges and proffer solutions. In 2014, the National Assembly of Nigeria made a bold move in the war against cybercrime when the Senate passed the Cybercrime Bill. This feat in addition to the cyber security strategy and policy documents introduced by the Office of the National Security Adviser (NSA) are attributes that will strengthen cyber security.
1.2 STATEMENT OF THE PROBLEM
The issue of cyber security is one that has been discussed by many people with various perspectives on the issue, most coming at it from different sides than the others. Cyber-crimes have gone beyond conventional crimes and now have threatening ramifications to the national security of all countries, even to technologically developed countries as the United States. The illegal act may be targeted at a computer network or devices e.g., computer virus, denial of service attacks (DOS), malware (malicious code). the illegal act may be facilitated by computer network or devices with target independent of the computer network or device”. However, ethical hacking has been used by various telecommunication companies to cover the loophole and this study is providing an overview on the issues and the solutions.
1.3 OBJECTIVES OF THE STUDY
The following are the objectives of this study:
1. To examine the issues of ethical hacking and cyber security in Nigeria telecommunication industry.
2. To examine the solutions to the issues of ethical hacking and cyber security in Nigeria telecommunication industry.
3. To determine the level of effectiveness of ethical hacking and cyber security in Nigerian telecommunication industry.
1.4 RESEARCH QUESTIONS
1. Is ethical hacking and cyber security practiced in Nigeria telecommunication industry?
2. What are the solutions to the issues of hacking and cyber crime in Nigeria telecommunication industry?
3. What is the level of effectiveness of ethical hacking and cyber security in Nigerian telecommunication industry?
1.6 SIGNIFICANCE OF THE STUDY
The following are the significance of this study:
1. The findings from this study will educate the stakeholders in the telecommunication industry and the general public on how ethical hacking can be used in cyber security to protect against cyber crime.
2. This research will be a contribution to the body of literature in the area of the effect of personality trait on student’s academic performance, thereby constituting the empirical literature for future research in the subject area.
1.7 SCOPE/LIMITATIONS OF THE STUDY
This study will cover the issues and solution relating to ethical hacking and cyber security in the Nigerian telecommunication industry.
LIMITATION OF STUDY
Financial constraint- Insufficient fund tends to impede the efficiency of the researcher in sourcing for the relevant materials, literature or information and in the process of data collection (internet, questionnaire and interview).
Time constraint- The researcher will simultaneously engage in this study with other academic work. This consequently will cut down on the time devoted for the research work.
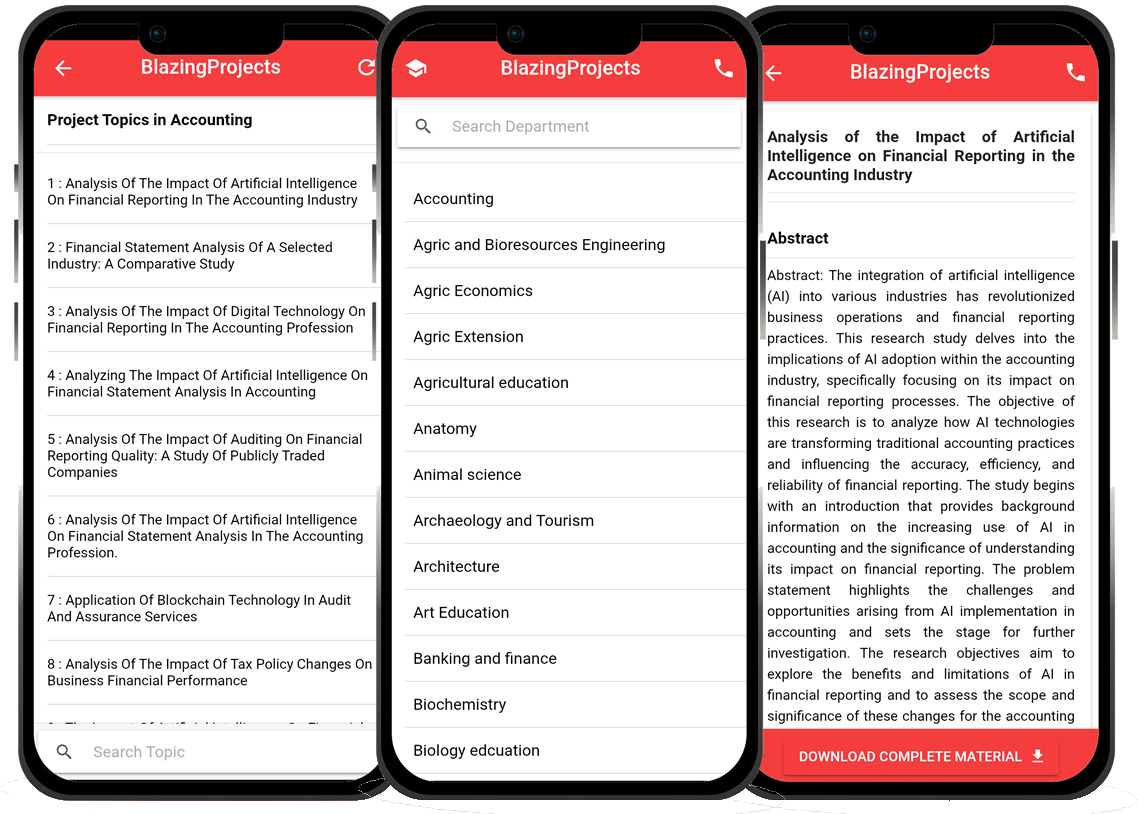
Blazingprojects Mobile App
📚 Over 50,000 Research Thesis
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Thesis-to-Journal Publication
🎓 Undergraduate/Postgraduate Thesis
📥 Instant Whatsapp/Email Delivery
Related Research
Development of a Personalized Adaptive Learning System for Computer Science Educatio...
The project titled "Development of a Personalized Adaptive Learning System for Computer Science Education" aims to address the need for personalized a...
The Impact of Virtual Reality Technology on Learning Outcomes in Computer Science Ed...
The research project titled "The Impact of Virtual Reality Technology on Learning Outcomes in Computer Science Education" aims to investigate the infl...
Design and Implementation of a Virtual Reality Simulation for Computer Science Educa...
The project titled "Design and Implementation of a Virtual Reality Simulation for Computer Science Education" aims to explore the potential benefits o...
Design and Development of an Interactive Virtual Reality Simulation for Computer Sci...
The project titled "Design and Development of an Interactive Virtual Reality Simulation for Computer Science Education" focuses on the utilization of ...
Development of an Interactive Learning Platform for Computer Science Education...
The project titled "Development of an Interactive Learning Platform for Computer Science Education" aims to revolutionize the way computer science edu...
Developing a Virtual Reality-based Educational Platform for Computer Science Learnin...
The research project titled "Developing a Virtual Reality-based Educational Platform for Computer Science Learning" aims to explore the potential of v...
Development of a Virtual Reality-Based Learning Environment for Computer Programming...
The project titled "Development of a Virtual Reality-Based Learning Environment for Computer Programming Education" aims to explore the integration of...
The Impact of Gamification on Student Engagement in Computer Science Education...
The project titled "The Impact of Gamification on Student Engagement in Computer Science Education" aims to investigate the effectiveness of incorpora...
Development of a Virtual Reality-based Learning Environment for Computer Programming...
The project titled "Development of a Virtual Reality-based Learning Environment for Computer Programming Education" aims to revolutionize the way comp...